Elena Kvochko serves as Chief Trust Officer at SAP and is a Board Director at Refugees International. At Cornell, Professor Kvochko teaches a graduate-level Cybersecurity for Business Organizations course. She has held senior executive leadership positions across banking and financial services, cloud, and software development industries, including previous roles as Senior Vice President and Technology Executive at Bank of America and as a divisional Chief Information Officer at Barclays Bank. An inventor with award-winning expertise in technology, digital transformation, and cybersecurity, Professor Kvochko has invented patent-pending technologies in cybersecurity, privacy, and secure financial technologies.

Cybersecurity
LeadershipCornell Certificate Program
Request More Info
Overview and Courses
Cybersecurity threats are inevitable, no matter your industry. It is now critical that business leaders equip themselves with cybersecurity knowledge, ensuring that their teams are prepared with the necessary strategies and tools to keep important data secure.
In this certificate program, you will gain the foundation required to protect your organization from cybersecurity threats. You’ll explore various types of threats that an organization may face as well as core company assets that need to be cataloged and protected. Throughout the courses, you will have the opportunity to practice identifying attacks, analyzing company security postures, understanding potential impacts, and strategizing methods to protect your organization. Finally, you will turn this knowledge into action by creating both internal and external communication plans, setting you up with applicable tools to bring back to your teams as you implement new strategies and lead your organization into a more secure future.
The courses in this certificate program are required to be completed in the order that they appear.
Course list
When it comes to cyber threats, every organization should strive to protect themselves and their users, and it is crucial to have a plan in place to protect your organization. Threats, whether big or small, have the potential to harm an organization, so understanding the digital threat landscape is critical for organizations to build effective security measures and risk mitigation strategies.
In this course, you will discover how to identify and classify cybersecurity threats to protect your organization. You will be introduced to different types of threats and vulnerabilities as well as the potential impacts each threat may have on organizational assets, gaining tools to help you identify these threats and minimize their impact. You will be introduced to cybersecurity frameworks, such as NIST, and best practices to protect possible targets within an organization. By the end of this course, you will have a foundation of the threat landscape to leverage to better protect your organization.
- May 13, 2026
- Aug 5, 2026
- Oct 28, 2026
There are different types of risks associated with the protection of assets, so understanding the significance of your assets will allow for planning ahead and budgeting realistically. Every organization needs to allocate spending on their cybersecurity budget based on their specific needs, but the allocation of cybersecurity budgets can vary depending on the industry and size of the organization.
In this course, you will analyze various company controls to better strategize about cybersecurity for your organization. You will start by identifying what needs to be protected and prioritizing investments. You will then be introduced to different types of controls and assets as well as common categories of budget allocations for cybersecurity. Finally, you will determine how your company's budget can be used for cybersecurity and identify ways to maximize your cybersecurity budget in order to protect your assets. By the end of this course, you will be equipped with practical skills, strategies, and approaches to make sound cybersecurity decisions.
You are required to have completed the following courses or have equivalent experience before taking this course:
- Analyzing Cybersecurity Threats
- May 27, 2026
- Aug 19, 2026
- Nov 11, 2026
Being able to evaluate the overall security status of your organization's product, sites, or teams at any point is critical, and conducting a thorough and applicable risk analysis is the key to this strategy.
In this course, you will assess an organization's security status to determine strengths and weaknesses. You will be introduced to the concept of security posture, and you will consider key areas to focus on when analyzing an existing security posture. You will also determine the best set of controls to strengthen security and better support weak spots to protect your organization. Finally, you will gain strategies for implementing future controls to protect your company, setting you up for success in risk analysis and planning efforts.
You are required to have completed the following courses or have equivalent experience before taking this course:
- Analyzing Cybersecurity Threats
- Assessing Cybersecurity Company Controls
- Mar 18, 2026
- Jun 10, 2026
- Sep 2, 2026
- Nov 25, 2026
Cyber communications are now ubiquitous across all types of organizations, but the necessary protections and policies surrounding their security are missing in many organizations. Every company needs to formulate policies related to privacy, cybersecurity, access, and information security for its internal and external users, and it is crucial to ensure that these policies are in line with applicable regulations, legal norms, and industry standards. Cyber communications are no exception.
In this course, you will discuss the key components of a cyber communications strategy. First, you will explore various relevant regulatory landscapes, both nationally and internationally. You will then identify who your audience is for internal and external communication plans. Finally, you will apply best practices to create both internal and external communication plans. By the end of this course, you will have new knowledge and practice to apply to your organization's policies and plans for cyber communications.
You are required to have completed the following courses or have equivalent experience before taking this course:
- Analyzing Cybersecurity Threats
- Assessing Cybersecurity Company Controls
- Conducting Cybersecurity Risk Analysis and Planning
- Apr 1, 2026
- Jun 24, 2026
- Sep 16, 2026
- Dec 9, 2026
Symposium sessions feature three days of live, highly interactive virtual Zoom sessions that will explore today’s most pressing topics. The Leadership Symposium offers you a unique opportunity to engage in real-time conversations with peers and experts from the Cornell community and beyond. Using the context of your own experiences, you will take part in reflections and small-group discussions to build on the skills and knowledge you have gained from your courses.
Join us for the next Symposium in which we’ll discuss the ways that leaders across industries have continued engaging their teams over the past two years while pivoting in strategic ways. You will support your coursework by applying your knowledge and experiences to relevant topics for leaders. Throughout this Symposium, you will examine different areas of leadership, including innovation, strategy, and engagement. By participating in relevant and engaging discussions, you will discover a variety of perspectives and build connections with your fellow participants from various industries.
All sessions are held on Zoom.
Future dates are subject to change. You may participate in as many sessions as you wish. Attending Symposium sessions is not required to successfully complete any certificate program. Once enrolled in your courses, you will receive information about upcoming events. Accessibility accommodations will be available upon request.
Request more Info by completing the form below.
How It Works
- View slide #1
- View slide #2
- View slide #3
- View slide #4
- View slide #5
- View slide #6
- View slide #7
- View slide #8
- View slide #9
Faculty Author
Key Course Takeaways
- Assess the potential impact of cybersecurity threats to your organization
- Discover core assets that need to be protected in your organization
- Plan, prepare, and strategize to protect your business from cyber attacks
- Prioritize company controls so you can identify the right protection measures and prioritize your investments
- Create internal and external communication plans for your security strategy

JOIN A LEADERSHIP SYMPOSIUM!
Download a Brochure
Not ready to enroll but want to learn more? Download the certificate brochure to review program details.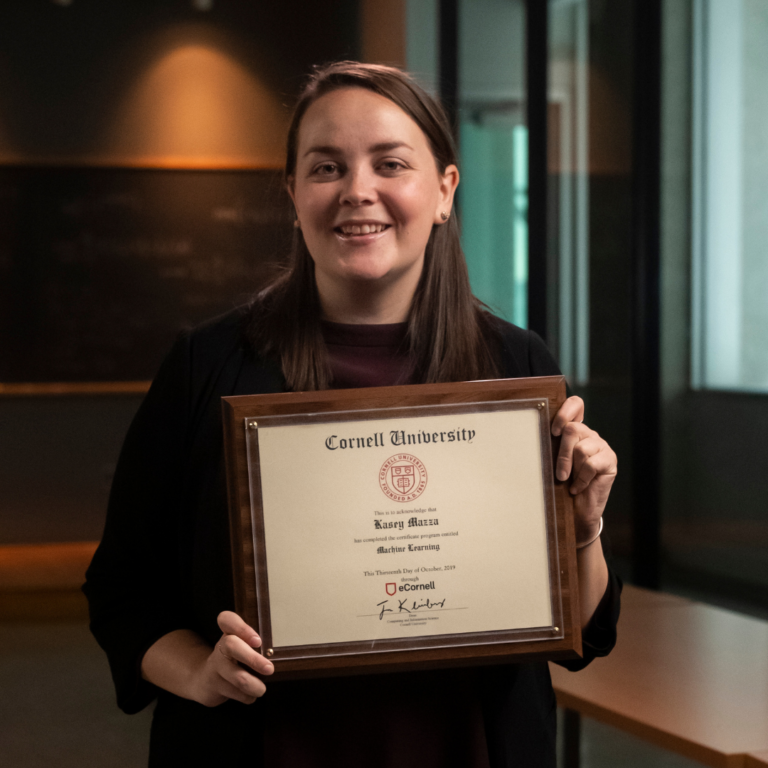

What You'll Earn
- Cybersecurity Leadership Certificate from Cornell Tech
- 40 Professional Development Hours (4 CEUs)
Watch the Video
Who Should Enroll
- C-suite executives
- Directors and managers
- Cybersecurity and privacy professionals
- Security analysts
- Developers
- Product and transformation leaders
- Veterans and others returning to the workforce
Request Information Now by completing the form below.

Cybersecurity Leadership
| Select Payment Method | Cost |
|---|---|
| $3,750 | |